Integrating StackHawk with Boost Security¶
StackHawk is a Dynamic Application Security Testing (DAST) tool built for developers. It runs HawkScan — a scanner that actively tests your running applications for real vulnerabilities and surfaces findings on the StackHawk platform where they can be analyzed and tracked to resolution.
Integrating StackHawk with Boost Security allows scan results from HawkScan to flow into Boost Security in real time via webhooks. Once connected, your StackHawk scan findings will appear alongside your other scanner data in Boost Security, giving you unified visibility across your application security posture.
Prerequisites¶
Before beginning the integration, ensure the following are in place:
- You have an active StackHawk account with access to your organization's settings.
- Your StackHawk organization is on a plan that supports the Webhook Integration. If you are unsure, contact StackHawk Support to confirm or enable it.
- You have sufficient permissions in both StackHawk and Boost Security to manage integrations and create API keys.
Integration Steps¶
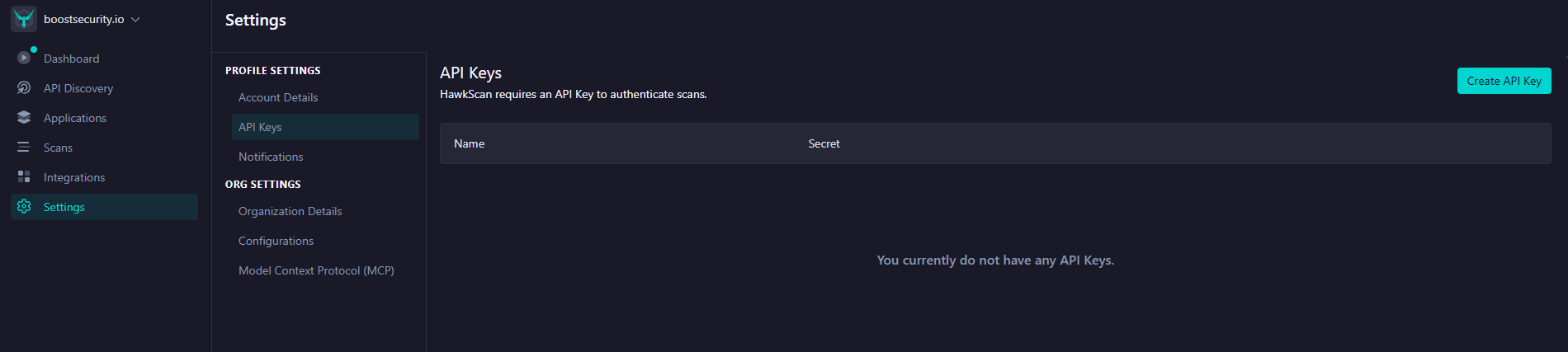
Step 1: Create a StackHawk API Key¶
Boost Security uses a StackHawk API key to authenticate with your StackHawk account during the integration setup. HawkScan itself also requires an API key to push scan results back to the StackHawk platform.
To create an API key:
- Log into your StackHawk account and navigate to Settings > API Keys, or go directly to https://app.stackhawk.com/settings/apikeys.
-
Click the Create API Key button in the top-right corner.
-
Give the key a descriptive name (for example,
boost-security-integration) and confirm creation. - Copy the generated API key and store it securely — it will not be shown again.
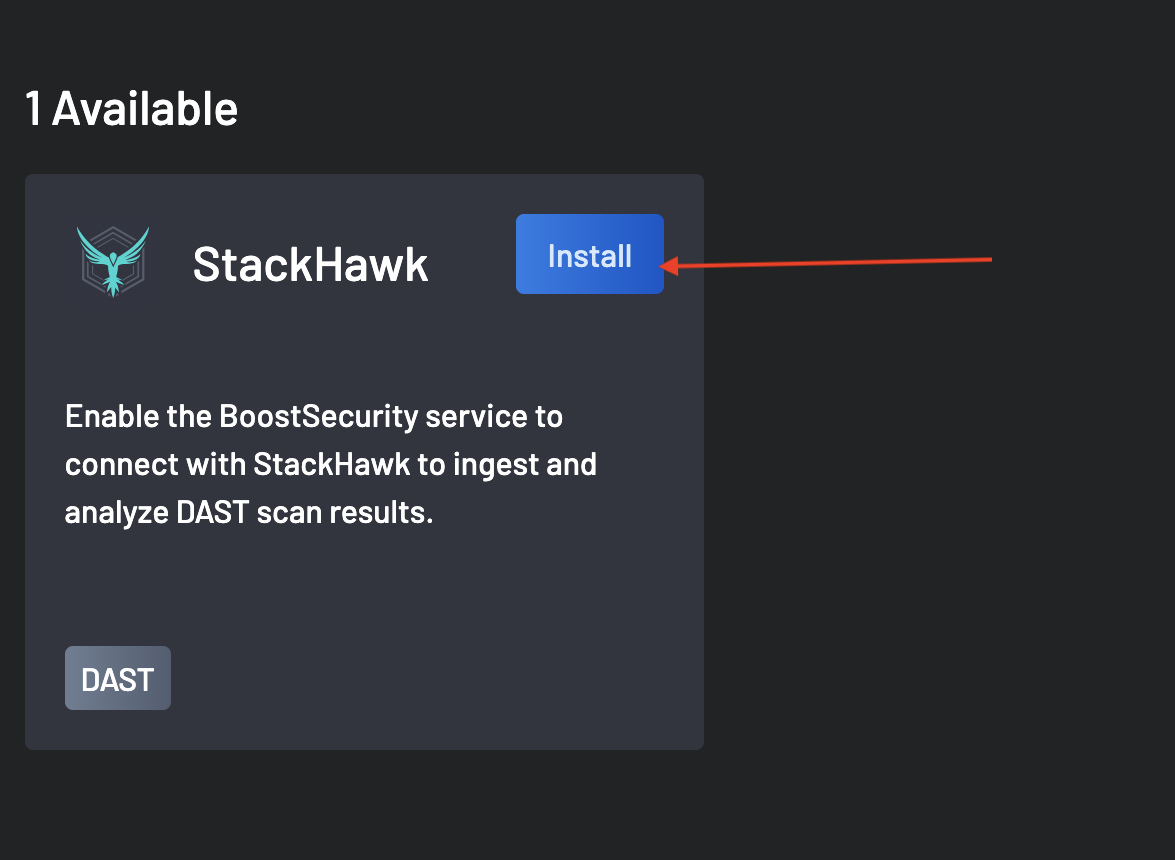
Step 2: Install the StackHawk Integration in Boost Security¶
With your API key ready, you can now connect StackHawk to Boost Security.
- In Boost Security, navigate to the Integrations page.
-
Locate StackHawk in the Available section and click the Install button next to it.
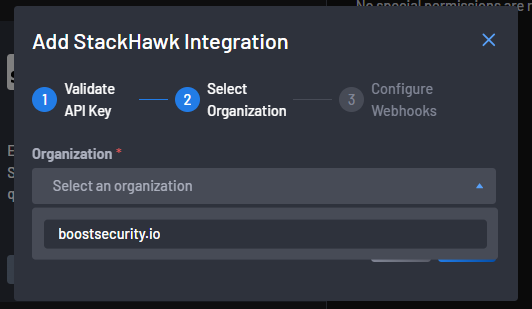
-
In the Add StackHawk Integration dialog that appears, paste the API key you created in Step 1 into the input field, then click Next to validate it.
If the key is invalid or has insufficient permissions, an error will be shown. Double-check that the key was copied correctly and that it belongs to the correct StackHawk account.
-
Once the API key is validated, you will be prompted to select your StackHawk organization. Choose the organization whose scan data you want to ingest into Boost Security and click Next.
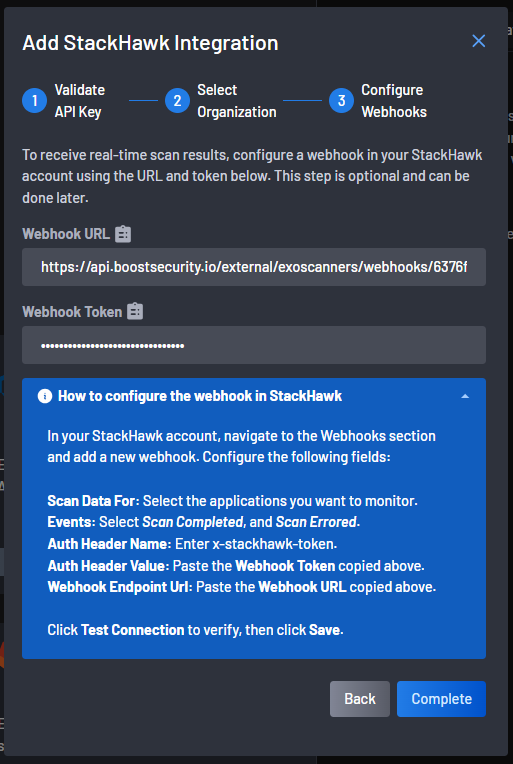
Step 3: Configure the Webhook in StackHawk¶
To receive real-time scan results from StackHawk, you need to register Boost Security as a webhook endpoint in your StackHawk account. Boost Security generates the Webhook URL and Webhook Token you will need for this step.
The Configure Webhooks step of the integration dialog displays both values:
Copy the Webhook URL and Webhook Token before proceeding.
Registering the Webhook in StackHawk¶
- In StackHawk, navigate to Integrations in the left-hand navigation and click Generic Webhook (or go directly to https://app.stackhawk.com/integrations).
- Click Add Webhook. A configuration panel will open.
-
Fill in the webhook fields as follows:
Field Value Name A descriptive name, e.g. Boost SecurityScan Data For Select the application(s) you want Boost Security to monitor, or choose Select All for all applications Events Select Scan Completed and Scan Errored Auth Header Name x-stackhawk-tokenAuth Header Value Paste the Webhook Token copied from Boost Security Webhook Endpoint URL Paste the Webhook URL copied from Boost Security -
Click Test Connection to verify that the webhook endpoint is reachable and responding correctly. StackHawk will send a test payload and display the response for debugging.
-
Once the test is successful, click Save and ensure the webhook is toggled to Enabled.
Note
Saved webhook responses are retained in StackHawk for later review or debugging if needed.
Step 4: Complete the Integration¶
Return to Boost Security and click the Complete button in the Add StackHawk Integration dialog to finalize the setup.
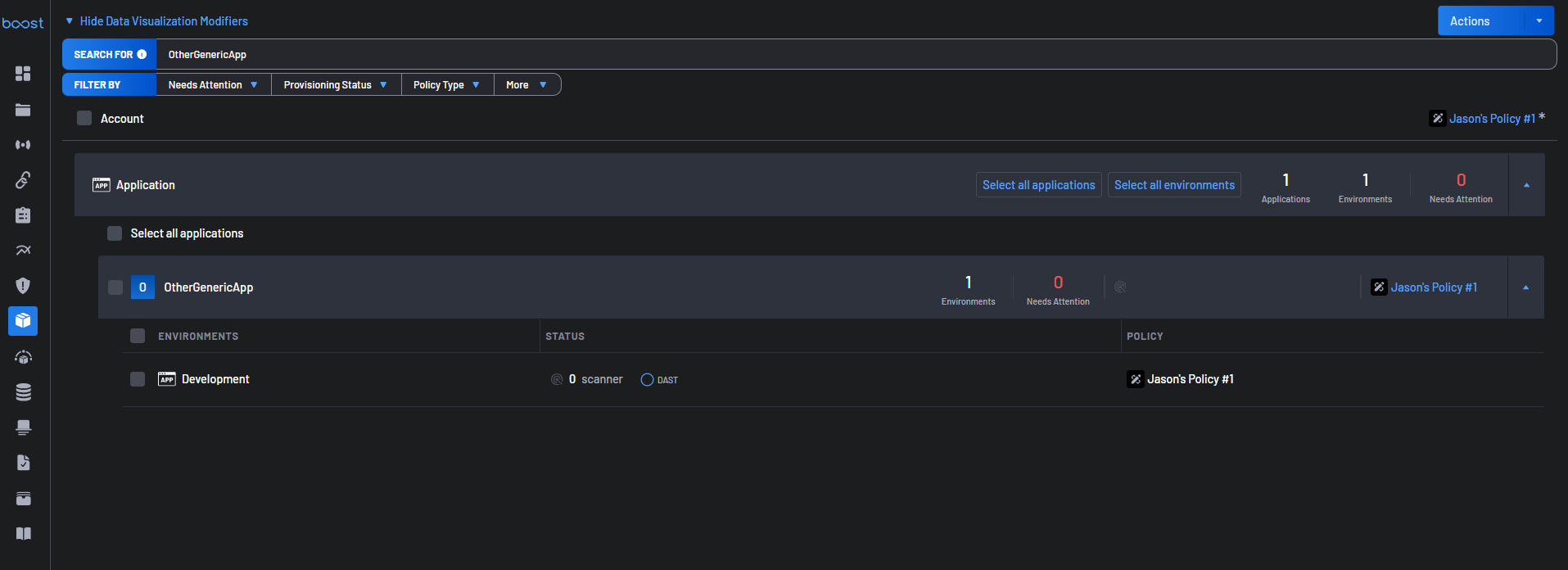
Once complete, Boost Security will begin receiving scan events from StackHawk whenever HawkScan runs against your configured applications. Scan results will appear in the Scans view, while the Scanner Coverage view is where the StackHawk DAST status is shown alongside any other configured scanners.
What Happens After Integration¶
Once the integration is active:
- Each time HawkScan completes or errors a scan on a monitored application, StackHawk sends a JSON payload to Boost Security via the configured webhook.
- The payload includes details about the scan run — its status, duration, findings by severity, and links back to the full scan report in StackHawk.
- Boost Security processes and surfaces this data within its application.
Note
Scan data only flows into Boost Security for events triggered after the webhook is enabled. Historical scans that ran before the integration was configured are not backfilled.
Troubleshooting¶
-
The API key validation fails. Ensure you have copied the full key without any leading or trailing whitespace. Verify the key was created in the correct StackHawk account and has not been revoked.
-
No scan data is appearing in Boost Security after integration. Confirm that the webhook in StackHawk is set to Enabled and that the Scan Data For field includes at least one application. Trigger a new HawkScan run and check StackHawk's webhook response log to verify the payload was sent and received a
200 OKresponse. -
The webhook test fails in StackHawk. Double-check that the Webhook Endpoint URL and Auth Header Value were copied exactly from the Boost Security dialog. Also confirm that no firewall or network policy is blocking outbound requests from StackHawk to Boost Security's API.
-
The StackHawk organization is not visible in Step 2. Your StackHawk plan may not include the Webhook Integration. Contact StackHawk Support to verify your plan and request enablement.