Endpoint Protection¶
The Endpoint Protection section in Boost Security provides centralized visibility and control over all software components installed across developer endpoints — browser extensions, IDE plugins, CLI agents, MCP servers, and packages. It is particularly useful for identifying shadow tools, unapproved extensions, and security exposure introduced at the developer workstation level.
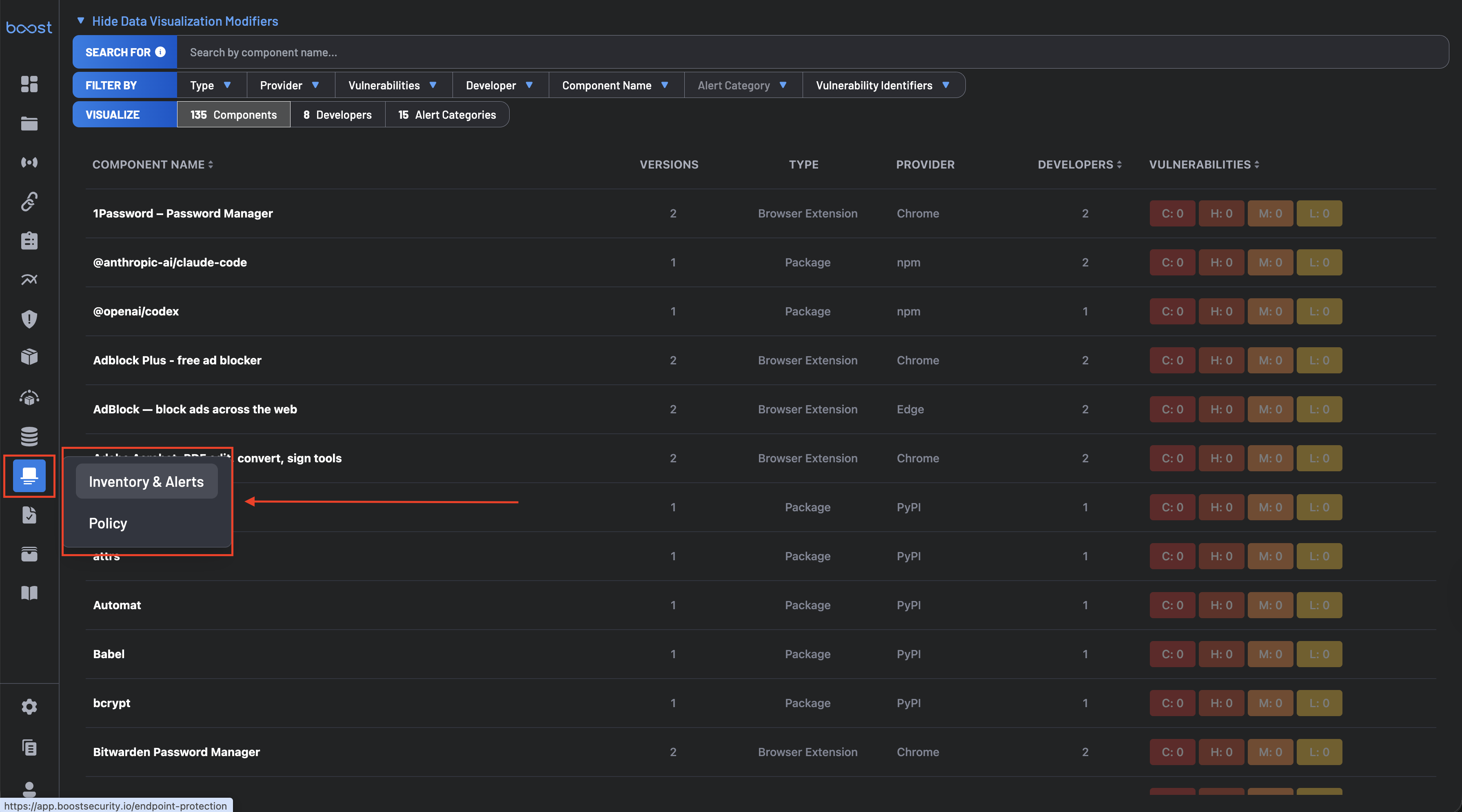
Endpoint Protection consists of two pages, accessible from the navigation panel:
- Inventory & Alerts – Browse, filter, and analyze detected endpoint components.
- Policy – Configure malware response actions and component allow/deny rules.
Installation¶
Endpoint Protection can be installed on endpoints in two ways:
- VS Code Extension – Install the Boost Security IDE extension from the Visual Studio Marketplace. This enables endpoint visibility directly from VS Code and also installs Boost's MCP server for more secure agentic coding.
- Script – Install Endpoint Protection with a script, ideal for endpoints that do not use VS Code or for broad deployment across multiple endpoints through EDR tools.
Inventory & Alerts¶
The primary interface for exploring endpoint component data across your organization.
Filters Panel¶
-
Search For – Search components by name using the search bar.
-
Filter By – Supports multi-select across: Type, Provider, Vulnerabilities, Developer, Component Name, Alert Category, and Vulnerability Identifiers.
- Type: Browser Extension, IDE Extension, CLI Agent, MCP Server, Package
- Provider: Chrome, Edge, Firefox, Brave, VS Code, Cursor, Jetbrains, CLI, MCP, npm, PyPI, Brew, Agent Skill, and more
-
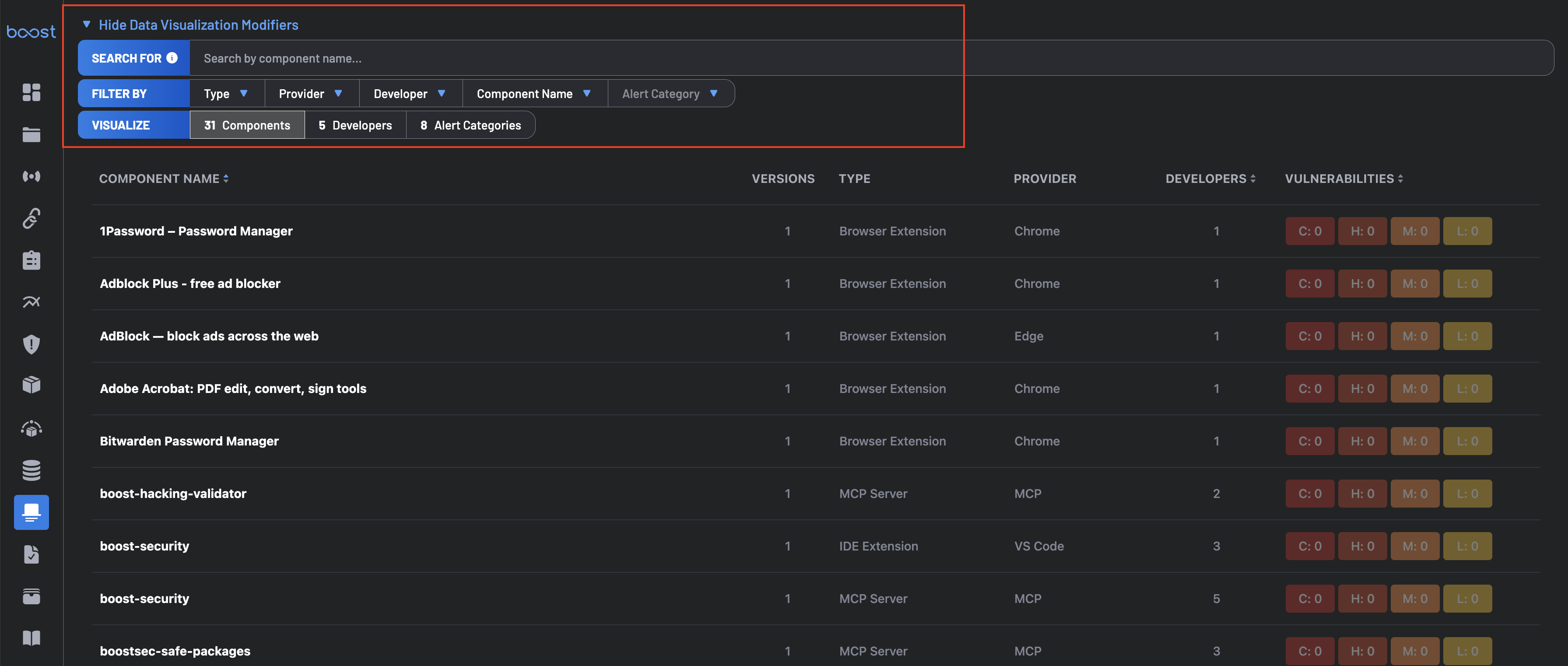
Visualize – Three clickable aggregated metrics that switch the main table view:
- Components – Total unique components detected. Returns to the default Component Table.
- Developers – Total developers with detected components. Switches to the Developers view.
- Alert Categories – Total distinct alert categories triggered. Switches to the Alert Categories view.
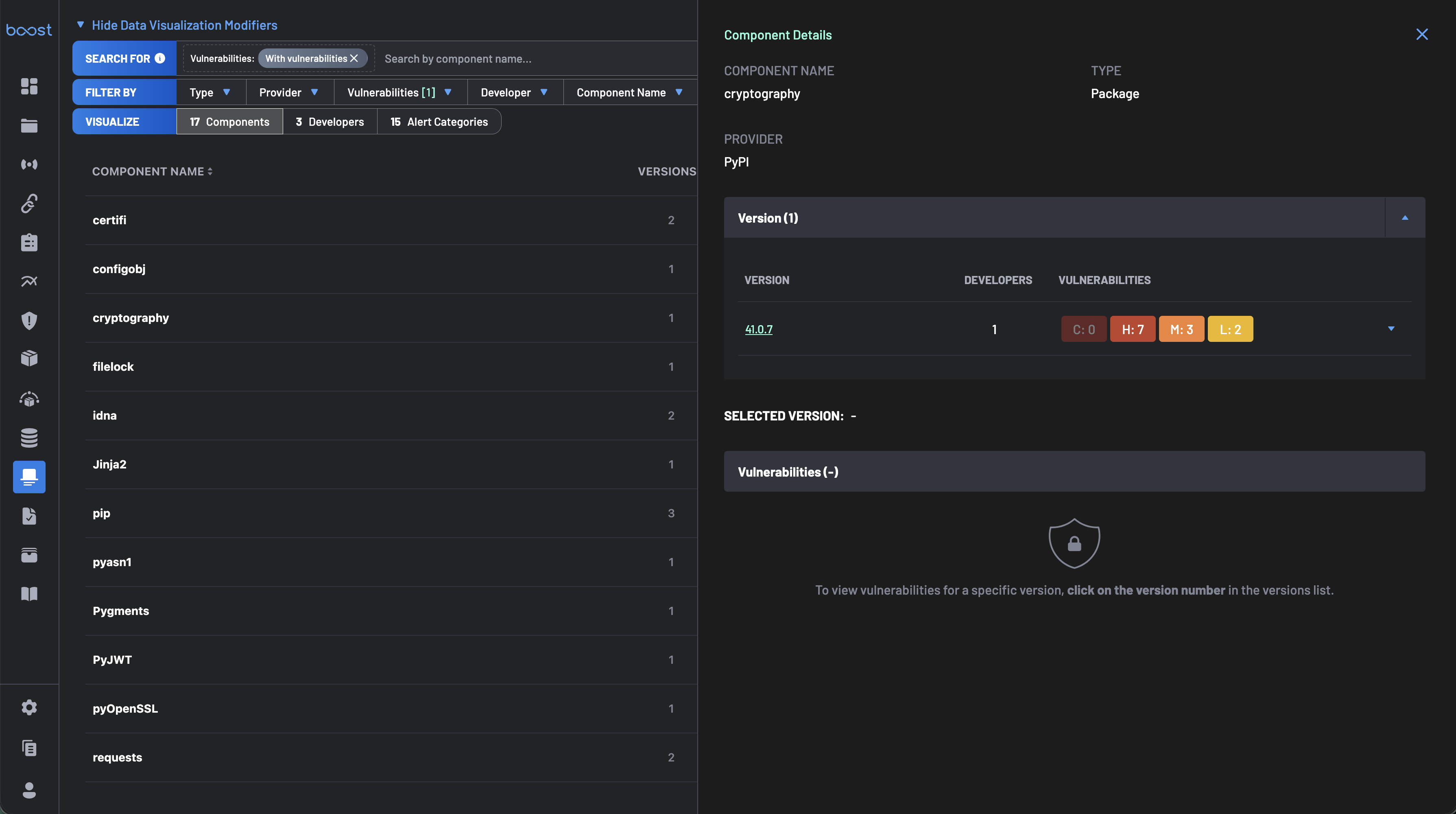
Component Table¶
Lists all detected endpoint software. Columns are sortable, vulnerability badges are color-coded, and rows are clickable for details.
- Component Name – Any endpoint software: browser extensions, IDE plugins, CLI agents, MCP servers, or packages.
- Versions – Installed version(s) of the component.
- Type – Browser Extension, IDE Extension, CLI Agent, MCP Server, or Package.
- Provider – Origin platform or ecosystem, e.g., Chrome, VS Code, MCP, npm.
- Developers – Number of users with the component installed.
- Vulnerabilities – Known CVEs by severity: C - Critical · H - High · M - Medium · L - Low
Clicking a row opens a Component Details panel showing the component name, type, provider, and a version-level breakdown of developer count and associated vulnerabilities per version — useful for identifying outdated installs and prioritizing remediation.
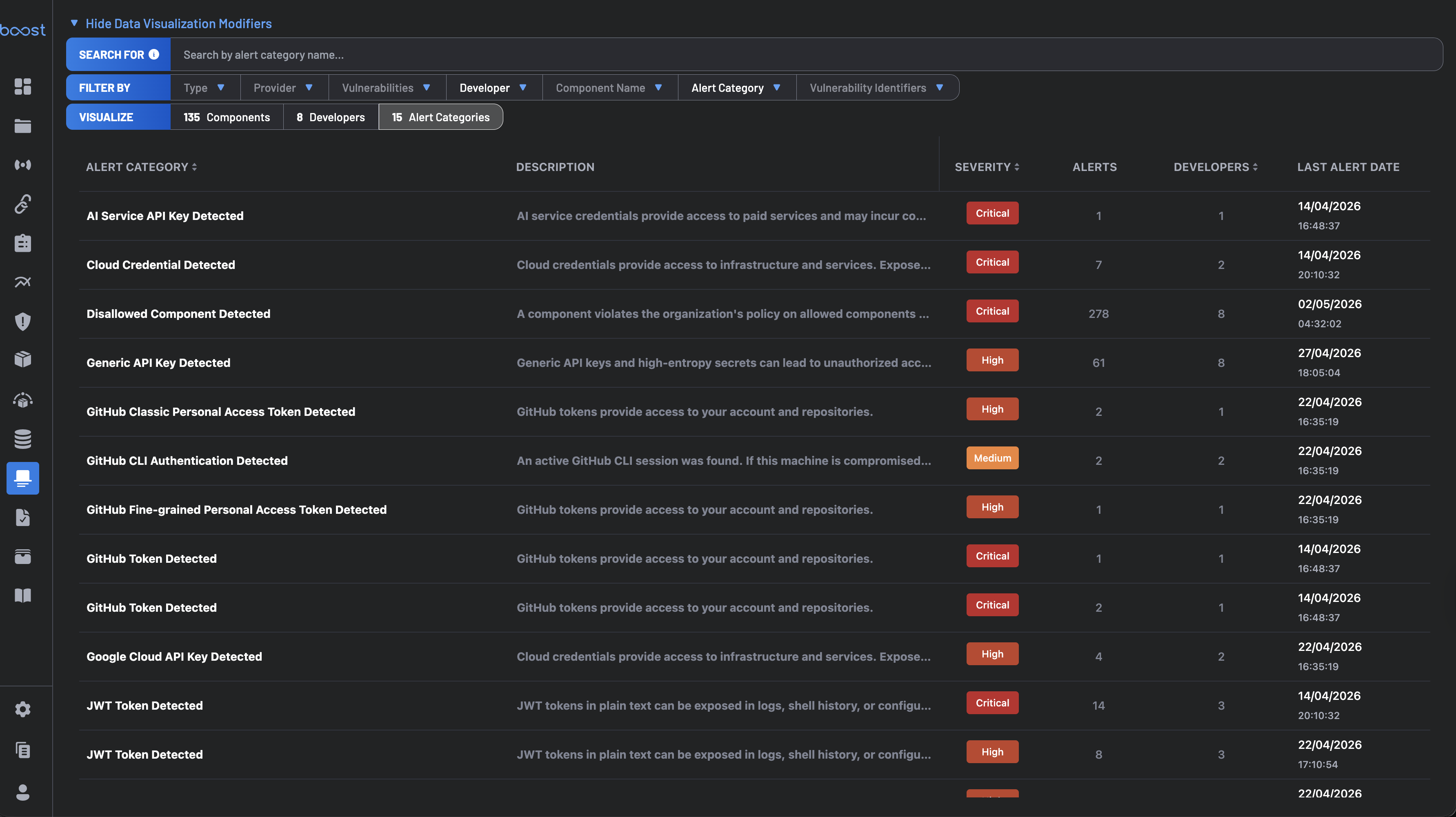
Alert Categories View¶
Clicking Alert Categories in the Visualize bar switches the table to a security-alert-centric view. The search bar updates to Search by alert category name....
Each row covers a distinct alert category with columns for Alert Category, Description, Severity, Alerts count, Developers count, and Last Alert Date. Rows are sortable.
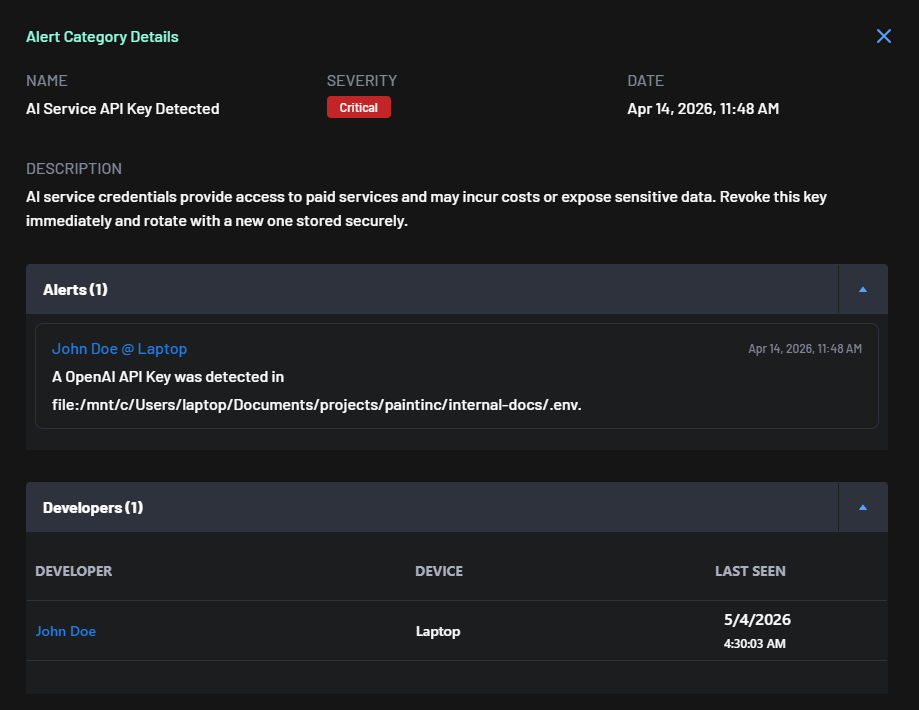
Clicking a row opens an Alert Category Details panel with the full risk description and remediation guidance, an Alerts list (developer @ device, timestamp, and exact file path where the issue was found), and a Developers list (developer, device, last-seen timestamp — each developer name is clickable to open Developer Details).
Developers View¶
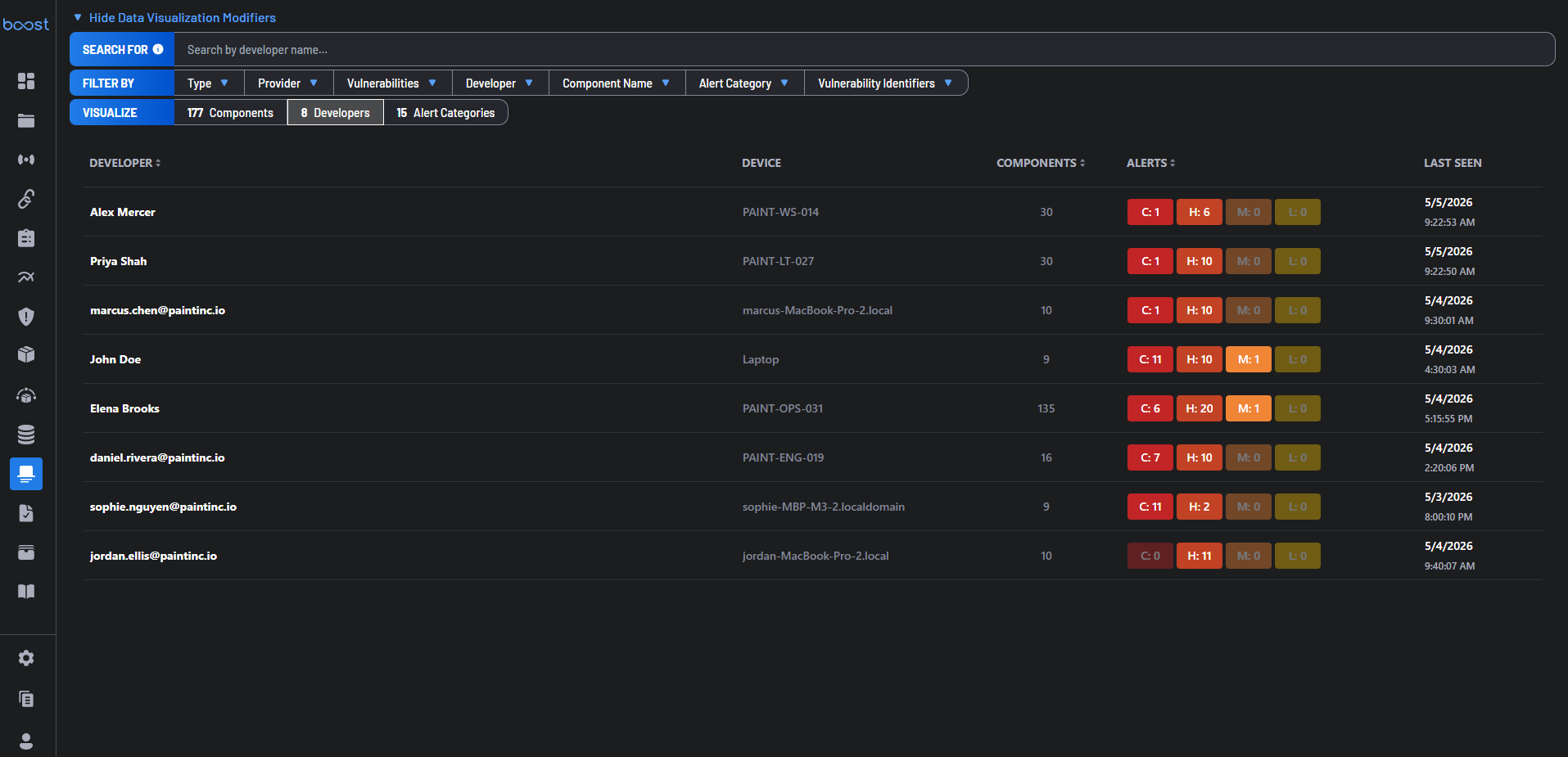
Clicking Developers in the Visualize bar switches the table to a developer-centric risk view. The search bar updates to Search by developer name....
Each row shows Developer, Device, Components count, Alerts by severity (C/H/M/L), and Last Seen. A developer may appear more than once if observed on multiple devices.
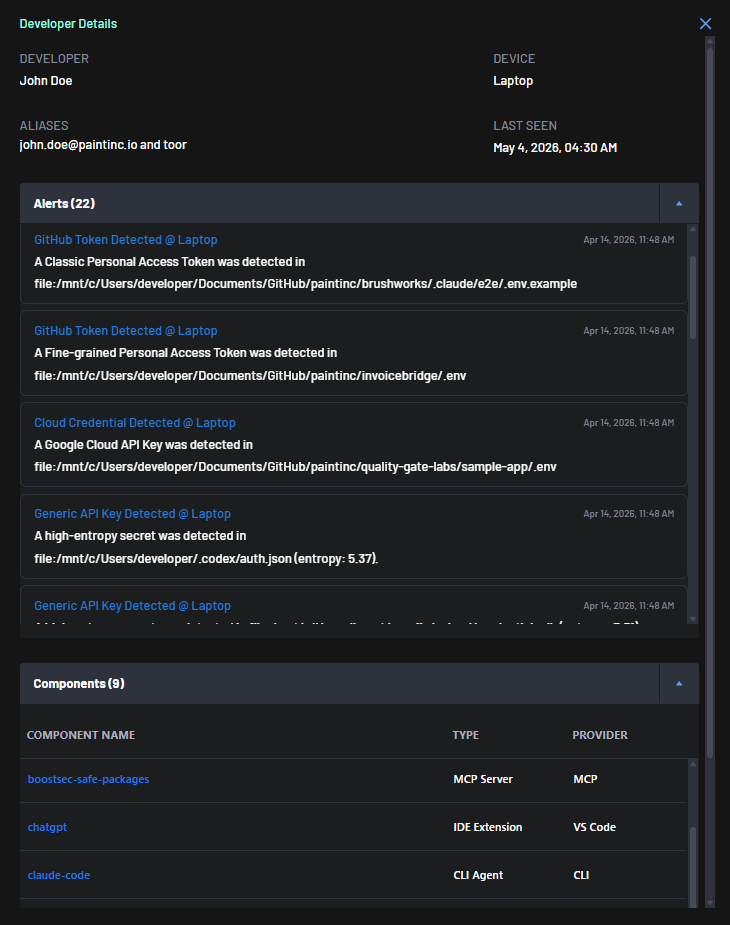
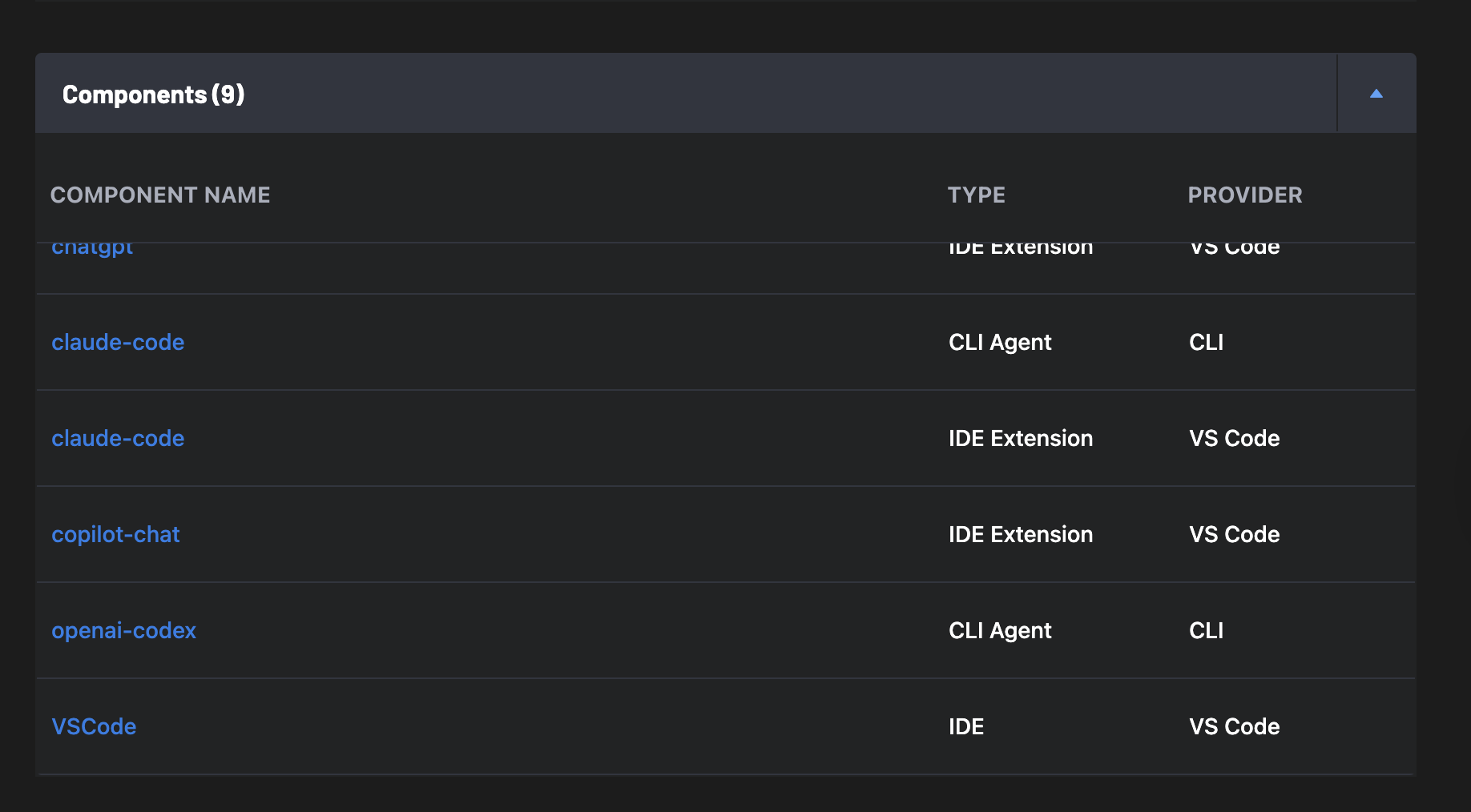
Clicking a row opens a Developer Details panel with:
- Header – Developer name, device, aliases (email addresses or system usernames), and last-seen timestamp.
- Alerts – Every alert on this developer's endpoints: alert type, device, timestamp, file path, and technical detail (e.g., entropy scores for detected secrets).
- Components – All endpoint software detected for this developer, showing component name, type, and provider.
Common Workflows¶
1. Identify High-Risk Components¶
- Navigate to Endpoint Protection > Inventory & Alerts
- Sort by Critical (C) or High (H) vulnerabilities
- Click a component to review version details and affected developers
2. Investigate Developer Exposure¶
- Click Developers in the Visualize bar
- Sort by Critical alerts to surface the highest-risk developers
- Click a developer to review their full alert history and installed components
3. Detect Unapproved Tools¶
- Filter by Provider or Type to narrow scope
- Scan for unknown or unauthorized tools
- Configure an Endpoint Protection Policy to enforce governance
Best Practices¶
- Regularly review components with Critical and High vulnerabilities
- Standardize approved tools across teams
- Monitor newly introduced components for risk
- Use filters to segment analysis by team or provider
- Configure an Endpoint Protection Policy to automate enforcement and malware response